'VPN'에 해당되는 글 3건
- 2008.11.05 Remote Access VPN Connections
- 2008.10.08 OpenVPN 설치및 사용하기 1
- 2008.10.08 OpenVPN 설정 방법
Remote AccessVPN Connections
For remote access VPN connections, a computer creates a remote access connection to a VPN server. During the connection process the VPN server assigns an IP address for the remote access VPN client and changes the default route on the remote client so that default route traffic is sent over the virtual interface.
IPAddresses and the Dial-Up VPN Client
For dial-up VPN clients who connect to the Internet before creating a VPN connection with a VPN server on the Internet, two IP addresses are allocated:
| ? | When creating the PPP connection, IPCP negotiation with the ISP NAS assigns a public IP address. |
| ? | When creating the VPN connection, IPCP negotiation with the VPN server assigns an intranet IP address. The IP address allocated by the VPN server can be a public IP address or private IP address, depending on whether your organization is implementing public or private addressing on its intranet. |
In either case, the IP address allocated to the VPN client must be reachable by hosts on the intranet and vice versa. The VPN server must have appropriate entries in its routing table to reach all the hosts on the intranet and the routers of the intranet must have the appropriate entries in their routing tables to reach the VPN clients.
The tunneled data sent through the VPN is addressed from the VPN client's VPN server-allocated address to an intranet address. The outer IP header is addressed between the ISP-allocated IP address of the VPN client and the public address of the VPN server. Because the routers on the Internet only process the outer IP header, the Internet routers forward the tunneled data to the VPN server's public IP address.
An example of dial-up client addressing is shown in Figure 9.14 where the organization uses private addresses on the intranet, and the tunneled data is an IP datagram.
Figure 9.14 Public and Private Addresses in PPTP Tunneled Data
DefaultRoutes and Dial-Up Clients
When a typical dial-up client dials the ISP, it receives a public IP address from the ISP NAS. A default gateway address is not allocated as part of the IPCP negotiation process. Therefore, in order to reach all Internet addresses, the dial-up client adds a default route to its routing table using the dial-up interface connected to the ISP. As a result, the client can forward the IP datagrams to the ISP NAS from where they are routed to its Internet location.
For dial-up clients with no other TCP/IP interfaces, this is the wanted behavior. However, this behavior can cause confusion for dial-up clients that have an existing LAN-based connection to an intranet. In this scenario, a default route already exists pointing to the local intranet router. When the dial-up client creates a connection with their ISP, the original default route remains in the routing table but is changed to have a higher metric. A new default route is added with a lower metric using the ISP connection.
As a result, the intranet locations that are not on the dial-up client's directly attached network are not reachable for the duration of the connection to the ISP. If the new default route is not created, all intranet locations are reachable, but Internet locations are not.
A Windows 2000?based dial-up client creates the default route by default.
To prevent the default route from being created
| ? | In the properties of the TCP/IP protocol of the dial-up connection object, in the Advanced TCP/IP Settings dialog box, click the General tab, and then clear the Use default gateway on remote network check box. |
To achieve connectivity to both intranet and Internet locations while the ISP connection is active, leave the Use default gateway on remote network option selected and add the routes of the intranet to the routing table of the dial-up client. The intranet routes can be added through static persistent routes using the route utility, or, if Routing Information Protocol (RIP) version 1 is being used as the intranet routing protocol, you can use the Route Listening Service to listen to RIP version 1 routing protocol traffic and dynamically add intranet routes. When connected to the ISP, all intranet locations are reachable using the intranet routes and all Internet locations are reachable using the default route.
Default Routes and VPNs over the Internet
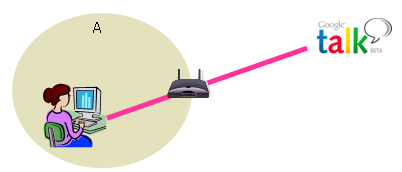
When the dial-up client calls the ISP, it adds a default route using the connection to the ISP as shown in Figure 9.15. At this point, it can reach all Internet addresses through the router at the ISP NAS.
Figure 9.15 Default Route Created When Dialing an ISP
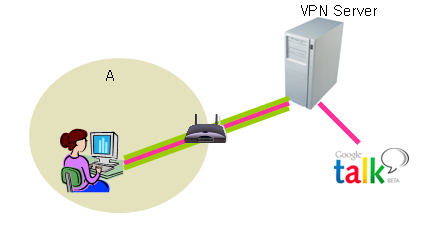
When the VPN client creates the VPN connection, another default route and a host route to the IP address of the tunnel server are added, as illustrated in Figure 9.16. The previous default route is saved but now has a higher metric. Adding the new default route means that all Internet locations except the IP address of the tunnel server are not reachable for the duration of the VPN connection.
Figure 9.16 Default Route Created When Initiating the VPN
Just as in the case of a dial-up client connecting to the Internet, when a dial-up VPN client using voluntary tunneling creates a VPN connection to a private intranet across the Internet, one of the following occurs:
| ? | Internet locations are reachable and intranet locations are not reachable when the VPN connection is not active. |
| ? | Intranet locations are reachable and Internet locations are not reachable when the VPN connection is active. |
For most Internet-connected VPN clients, this behavior does not represent a problem because they are typically engaged in either intranet or Internet communication, not both.
For VPN clients who want concurrent access to intranet and Internet resources when the VPN is connected, the solution depends on the nature of the IP addressing in the intranet. In all cases, configure the VPN connection object so that it does not add a default gateway. When the VPN connection is created, the default route remains pointed to the ISP NAS, allowing access to all Internet addresses.
Based on the type of intranet addressing you use, enable concurrent access to intranet and Internet resources as follows:
Public Addresses Add static persistent routes for the public network IDs of the intranet using the IP address of the VPN server's virtual interface as the gateway IP address.
Private Addresses Add static persistent routes for the private network IDs of the intranet using the IP address of the VPN server's virtual interface as the gateway IP address.
Overlapping or Illegal Addresses If the intranet is using overlapping or illegal addresses (IP network IDs that are not private and have not been registered by Internet Network Information Center [InterNIC] or obtained from an ISP), those IP addresses might be duplicated by public addresses on the Internet. If static persistent routes are added on the VPN client for the overlapping network IDs of the intranet, the locations on the Internet for the overlapping addresses are not reachable.
In each of these cases, static persistent routes for the network IDs of the intranet need to be added to the VPN client. When the persistent routes are added, they are saved in the registry. With Windows NT 4.0 Service Pack 3 and later and with Windows 2000, the persistent routes are not actually added to the IP routing table (and are not visible with the route print command at the Windows 2000 command prompt) until the IP address of the gateway is reachable. The IP address of the gateway becomes reachable when the VPN connection is made.
For each route, type the following route utility syntax at a Windows 2000 command prompt:
ROUTE ADD <Intranet Network ID> MASK <NetMask> <IP address of VPN server's virtual interface> -p
The gateway IP address in the route commands for each intranet route is the IP address assigned to the VPN server's virtual interface, not the IP address of the VPN server's Internet interface.
You can determine the IP address of the VPN server's virtual interface from the IP address of the Internal interface under IP Routing - General in the Routing and Remote Access snap-in. If you use DHCP to obtain IP addresses for dial-up networking and VPN clients, the IP address of the VPN server's virtual interface is the first IP address obtained when requesting DHCP addresses. If you have configured a static IP address pool, the IP address of the VPN server's virtual interface is the first IP address in the static IP address pool. You can also determine the IP address of the VPN server's virtual interface by double-clicking the virtual private networking connection object when the VPN connection is active. In the resulting Status dialog box, click the Details tab.
![]()
Caution
For all of these cases, you must add the routes very carefully to ensure that the private traffic to the intranet is forwarded using the VPN connection and not the PPP connection to the ISP. If the wrong routes are added, the traffic that you intend to forward across the VPN in an encrypted form is instead sent unencrypted across the Internet. For example, if your intranet is using the public network ID 207.46.130.0/24 (subnet mask 255.255.255.0), and you mistakenly add a persistent static route for 207.46.131.0/24, all traffic to the intranet network 207.46.130.0/24 is forwarded across the Internet in plaintext, rather than being encrypted and sent across the VPN connection.
Source : MS TechNet
OpenVPN 설치및 사용하기 ¶
1.1 시작하며 ¶
1.2 VPN 이란 ¶
1.3 OpenVPN ¶
- Slashdot | Free SSL VPN Solutions? (http://ask.slashdot.org/article.pl?sid=06/09/26/228241)
- Slashdot | VPN Solutions for Distributed Installations? (http://ask.slashdot.org/article.pl?sid=06/04/13/1716227)
- Slashdot | Low Cost VPN Solutions? (http://ask.slashdot.org/article.pl?sid=05/01/03/1617208)
1.3.1 간단한 동작 원리 ¶
1.4.1 설치 하기 ¶
tar xfz openvpn-[version].tar.gz
cd openvpn-[version]
./configure --prefix=/usr/local/openvpn
make
make install
1.4.2 열쇠 만들기 ¶
# These are the default values for fields # which will be placed in the certificate. # Don't leave any of these fields blank. export KEY_COUNTRY=US export KEY_PROVINCE=MA export KEY_CITY=Cambridge export KEY_ORG="OpenVPN-Server" export KEY_EMAIL="hunkim@gmail.com"
./build-key-server server
# ./build-dh Generating DH parameters, 1024 bit long safe prime, generator 2 This is going to take a long time .................+........................................... ...................+.............+.................+......... ......................................
./build-key hunkim
* Sign the certificate? [y/n] * 1 out of 1 certificate requests certified, commit? [y/n]
| Filename | Needed By | Purpose | Secret |
| ca.crt | server + all clients | Root CA certificate | NO |
| ca.key | key signing machine only | Root CA key | YES |
| dh{n}.pem | server only | Diffie Hellman parameters | NO |
| server.crt | server only | Server Certificate | NO |
| server.key | server only | Server Key | YES |
| hunkim.crt | hunkim only | hunkim Certificate | NO |
| hunkim.key | hunkim only | hunkim Key | YES |
여기서 Secret가 YES된 열쇠들은 알아서 잘 보관하기 바란다. 아니면 VPN서버와 클라이언트 사이에 패킷을 엿듣는 middle-man 공격이 가능해진다.
1.4.3 환경설정 ¶
 여기서 주의할 점은, 서버가 UDP를 쓰면 클라이언트도 UDP를 쓰도록 설정해야 한다는 것이다.
여기서 주의할 점은, 서버가 UDP를 쓰면 클라이언트도 UDP를 쓰도록 설정해야 한다는 것이다. # server.conf # Any X509 key management system can be used. # OpenVPN can also use a PKCS #12 formatted key file # (see "pkcs12" directive in man page). ca keys/ca.crt cert keys/server.crt key keys/server.key # This file should be kept secret # Diffie hellman parameters. # Generate your own with: # openssl dhparam -out dh1024.pem 1024 # Substitute 2048 for 1024 if you are using # 2048 bit keys. dh keys/dh1024.pem
1.4.4 실행 ¶
# /sbin/openvpn server.conf Wed Dec 27 04:06:51 2006 OpenVPN 2.0.9 i686-intel-linux [SSL] [LZO] [EPOLL] built on Dec 26 2006 Wed Dec 27 04:06:51 2006 Diffie-Hellman initialized with 1024 bit key Wed Dec 27 04:06:51 2006 TLS-Auth MTU parms [ L:1542 D:138 EF:38 EB:0 ET:0 EL:0 ] Wed Dec 27 04:06:51 2006 TUN/TAP device tun0 opened Wed Dec 27 04:06:51 2006 /sbin/ifconfig tun0 10.8.0.1 pointopoint 10.8.0.2 mtu 1500 Wed Dec 27 04:06:51 2006 /sbin/route add -net 10.8.0.0 netmask 255.255.255.0 gw 10.8.0.2 Wed Dec 27 04:06:51 2006 Data Channel MTU parms [ L:1542 D:1450 EF:42 EB:135 ET:0 EL:0 AF:3/1 ] Wed Dec 27 04:06:51 2006 UDPv4 link local (bound): [undef]:1194 Wed Dec 27 04:06:51 2006 UDPv4 link remote: [undef] Wed Dec 27 04:06:51 2006 MULTI: multi_init called, r=256 v=256 Wed Dec 27 04:06:51 2006 IFCONFIG POOL: base=10.8.0.4 size=62 Wed Dec 27 04:06:51 2006 IFCONFIG POOL LIST Wed Dec 27 04:06:51 2006 hunkim,10.8.0.4 Wed Dec 27 04:06:51 2006 Initialization Sequence Completed
1.5 클라이언트 ¶
1.5.1 설치하기 ¶

1.5.2 키 복사하기 ¶
1.5.3 환경설정 ¶
... # The hostname/IP and port of the server. # You can have multiple remote entries # to load balance between the servers. remote vpn.mit.edu 1194 ...
... # SSL/TLS parms. # See the server config file for more # description. It's best to use # a separate .crt/.key file pair # for each client. A single ca # file can be used for all clients. ca "C:\\Program Files\\OpenVPN\\config\\ca.crt" cert "C:\\Program Files\\OpenVPN\\config\\hunkim.crt" key "C:\\Program Files\\OpenVPN\\config\\hunkim.key" ...
# Use the same setting as you are using on the server. On most systems, the # VPN will not function unless you partially or fully disable the firewall # for the TUN/TAP interface. ;dev tap dev tun .... # Are we connecting to a TCP or UDP server? Use the same setting as # on the server. ;proto udp proto tcp ...이것으로 클라이언트의 모든 설정은 끝이 났다.
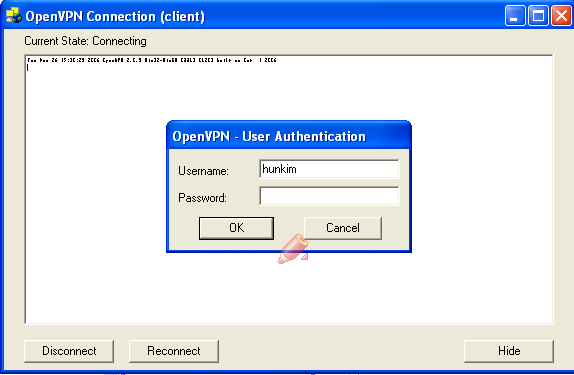
1.5.4 서버연결 ¶
Tue Dec 26 15:32:45 2006 Cannot load CA certificate file C:\Program Files\OpenVPN\config\ca.crt (SSL_CTX_load_verify_locations): error:02001002:system library:fopen:No such file or directory: error:2006D080:BIO routines:BIO_new_file:no such file: error:0B084002:x509 certificate routines:X509_load_cert_crl_file:system lib Tue Dec 26 15:32:45 2006 Exiting
$ ping 10.8.0.1 PING 10.8.0.1 (10.8.0.1): 56 data bytes 64 bytes from 10.8.0.1: icmp_seq=0 ttl=64 time=260 ms 64 bytes from 10.8.0.1: icmp_seq=1 ttl=64 time=216 ms ----10.8.0.1 PING Statistics---- 2 packets transmitted, 2 packets received, 0.0% packet loss round-trip (ms) min/avg/max/med = 216/238/260/238
server $ ping 10.8.0.6 PING 10.8.0.1 (10.8.0.6): 56 data bytes ...
1.6.1 추가적 사용자 인증 ¶
plugin /usr/share/openvpn/plugin/lib/openvpn-auth-pam.so login
1.6.1.1 사용자/비밀번호 만으로 인증하기 ¶
... client-cert-not-required username-as-common-name ...
... ca "C:\\Program Files\\OpenVPN\\config\\my-server.ca.crt" ...
1.6.2 서버쪽의 다른 서버들 연결하기 (도움 필요) ¶
push "route 128.30.0.0 255.255.255.0"
On Linux, use the command:
echo 1 > /proc/sys/net/ipv4/ip_forward
# Allow TUN interface connections to OpenVPN server iptables -A INPUT -i tun+ -j ACCEPT # Allow TUN interface connections to be forwarded through other interfaces iptables -A FORWARD -i tun+ -j ACCEPT
1.6.3 전체 트래픽을 서버로 라우팅 하기 ¶
# If enabled, this directive will configure # all clients to redirect their default # network gateway through the VPN, causing # all IP traffic such as web browsing and # and DNS lookups to go through the VPN # (The OpenVPN server machine may need to NAT # the TUN/TAP interface to the internet in # order for this to work properly). # CAVEAT: May break client's network config if # client's local DHCP server packets get routed # through the tunnel. Solution: make sure # client's local DHCP server is reachable via # a more specific route than the default route # of 0.0.0.0/0.0.0.0. push "redirect-gateway def1"
On Linux, use the command:
echo 1 > /proc/sys/net/ipv4/ip_forward
iptables -t nat -A POSTROUTING -s 10.8.0.0/24 -o eth0 -j MASQUERADE
push "dhcp-option DNS 10.8.0.1"
Ethernet adapter Local Area Connection 7:
Connection-specific DNS Suffix . :
Description . . . . . . . . . . . : TAP-Win32 Adapter V8
Physical Address. . . . . . . . . : 00-FF-51-C4-40-4B
Dhcp Enabled. . . . . . . . . . . : Yes
Autoconfiguration Enabled . . . . : Yes
IP Address. . . . . . . . . . . . : 10.8.0.6
Subnet Mask . . . . . . . . . . . : 255.255.255.252
Default Gateway . . . . . . . . . : 10.8.0.5
DHCP Server . . . . . . . . . . . : 10.8.0.5
DNS Servers . . . . . . . . . . . : 10.8.0.1
Lease Obtained. . . . . . . . . . : Tuesday, December 26, 2006 4:43:57 PM
Lease Expires . . . . . . . . . . : Wednesday, December 26, 2007 4:43:57 PM
// 기존의 default gateway 를 제거 route DELETE 0.0.0.0 // VPN_SERVER_IP 를 gateway 로 잡는다. 이때 중요한 것은 P-2-P 의 VPN 측 IP // 로 잡아야 한다. 아무생각 없이 VPN server 의 real IP 를 잡으면 대략 낭패다. // // OpenVPN 은 route 방식과 bridge 방식이 있는데, 두가지 모드 중에서 VPN_SERVER_IP // 는 다음과 같다. // // * route 방식 // 서버측에 "server 192.168.100.0 255.255.255.0" 라는 설정이 있다면 192.168.100.1 // 로 설정을 하면 될 것이다. route 방식은 필자가 직접 한 것이 아니라 추측이다. // // * bridge 방식 // 서버측에 "server-bridge 192.168.100.1 255.255.255.0 192.168.100.2 192.168.100.254" // 와 같이 설정이 되어 있다면 192.168.100.1 로 사용하면 된다. route ADD 0.0.0.0 MASK 0.0.0.0 VPN_SERVER_IP
1.7 마치면서 ¶
원본 : http://wiki.kldp.org/wiki.php/OpenVPN#s-1
1 프로그램 다운로드
윈도우즈 용은 OpenVPN GUI로, 다운로드는 다음과 같다.
http://openvpn.se/download.html
프로그램 다운로드 : http://openvpn.se/files/install_packages/openvpn-2.0.9-gui-1.0.3-install.exe
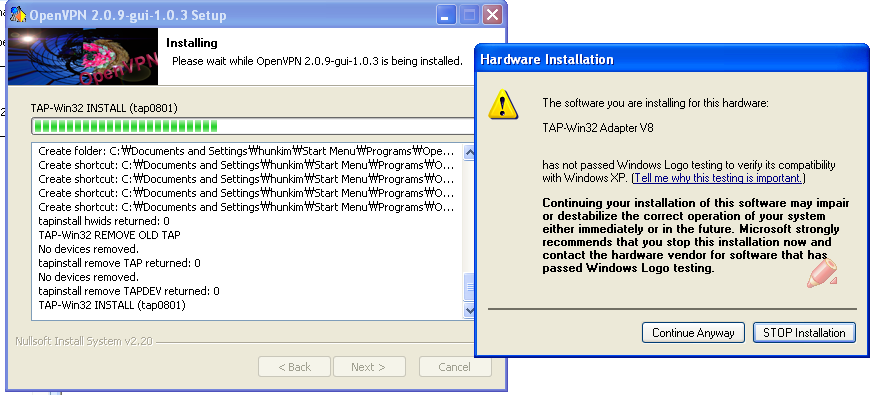
2. 설치
기본 설치로 하면 Program File\OpenVPN에 깔린다.
3. 키 설정 (http://openvpn.net/howto.html#pki)
1) 준비
- 커맨드 쉘로 \Program Files\OpenVPN\easy-rsa 폴더로 이동
init-config
vars
clean-all
2) 기본 ca 작성
(입력을 편하게 하려면 vars.bat파일의 set KEY_COUNTRY=US등의 내용을 변경하세요... 안해도 무방)
build-ca
다음과 같이 물어봅니다.
Country Name (2 letter code) [KG]:
State or Province Name (full name) [NA]:
Locality Name (eg, city) [BISHKEK]:
Organization Name (eg, company) [OpenVPN-TEST]:
Organizational Unit Name (eg, section) []:
Common Name (eg, your name or your server's hostname) []:OpenVPN-CA
Email Address [me@myhost.mydomain]:
여기는 적당히 채우세요~
다만 Common Name은 앞으로 만들 키에서 전체적으로 중복되면 안됩니다.
3) 서버 키 작성
build-key-server server
앞에 입력한 것과 비슷하게 나옵니다. Common Name만 다르게 하시고
나머지는 똑같이 입력하세요.
y/n 묻는 건 당연히 y겠죠.
4)클라이언트 키 작성
build-key client1
동시에 여러 클라이언트가 접속한다면 동접 갯수만큼 client1를 숫자나 적당한 것으로 바꿔서 키를 만들면 됩니다. client1를 원하는 이름으로 바꾸세요.
예를 들어 세명이 동시에 사용한다면
build-key client1
build-key client2build-key client3
이런식으로 만들어 주면 되겠죠.
그리고 처음 키를 만들때와 같은 걸 물어보는데 Common name에 client1같은 각각의 이름을 넣어주면 됩니다.
4. DH parameter 생성
build-dh
5. ta 키 생성
keys 디렉토리로 이동해서..
openvpn --genkey --secret ta.key 라고 하면 ta.key가 만들어집니다.
6. key 파일 복사.
config 폴더에 다음과 같은 파일을 복사합니다.
ca.crt
ca.key
dh1024.pem
server.crt
server.key
ta.key
7. Server config 설정
1) sample-config 폴더에서 server.ovpn 파일을 config 폴더로 복사합니다.
2) 복사한 server.ovpn 파일을 메모장으로 열어서 다음 항목을 찾아 필요한 값을 설정합니다.
port
proto
tls-auth ta.key 0
cipher BF-CBC
port는 원하는 포트번호를 proto는 udp나 tcp를 설정합니다.
tls-auth, cipher 는 앞에 있는 커맨트 ; 를 지워줍니다.
설정이 되었으면 저장하세요.
8. 서버 실행
config 폴더에서 openvpn server.ovpn 이라고 입력합니다.
나오는 내용을 확인해 보시고..에러가 없으면 F3인가 F4인가를 눌러 종료합니다.
그리고 제어판->관리도구->서비스 에서 OpenVPN 서비스를 자동으로 하시고 시작 하시면 컴퓨터가 부팅될 경우 자동으로 실행이 됩니다.
9. 클라이언트 설정
1) 서버와 똑같이 프로그램을 설치합니다. (같은 프로그램으로 서버와 클라이언트를 사용함)
2) 위의 서버에서 만든 다음과 같은 키 파일을 config 폴더에 복사합니다.
ca.crt
ca.key
client1.key
client1.crt
ta.key
3) sample-config 폴더에서 client.ovpn을 config 폴더로 복사합니다.
이때 client.ovpn을 client1.ovpn으로 이름을 맞춰 주는 게 좋습니다.
(여러곳의 연결설정을 할때 편함)
4) client.ovpn을 메모장으로 열어서 다음 항목을 수정합니다.
proto
remote
cert
key
tls-auth
cipher
; proto는 서버에서 설정한 것으로 udp/tcp로 맞춰주시고, remote는 remote 서버ip 포트번호 로 하시면 됩니다.
cert는 client1.crt
key는 client1.key 로 파일 이름을 맞춰 주세요.
tls-auth는 앞의 ;를 지워주시고
cipher도 서버와 같이 cipher BF-CBC로 맞춰 주시면 됩니다.
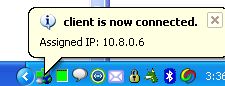
5) 연결 확인
openvpn client1.ovpn으로 해보시면 되고
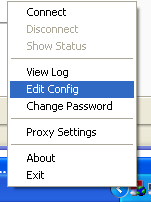
평상시에는 오른쪽 아래의 트레이에 있는 OpenVPN GUI의 오른쪽 클릭을 하면
Connect가 나옵니다. 문제없이 연결되면 아이콘이 초록색으로 변경됩니다.
6) 서버 접속
서버의 ip를 변경할수 있지만 여기서는 기본 설정이므로 10.8.0.1이 서버의 ip입니다.
ping을 해보시던가..리모트 접속을 해보시면 틀린거 없이 하셨다면 연결이 될껍니다.

![[http]](http://wiki.kldp.org/imgs/http.png)


